Despite an ever-changing digital world, email has held strong as a popular form of communication for the dental community. Email targeting has allowed cybercriminals to excel at their craft and develop new and creative ways to scam you out of personal and potentially sensitive information. Today, we'll cover how to prevent phishing scams and other cyber attacks by tackling one of the most common mediums used – links. Learning this will help your team avoid phishing scams and other cyberattacks that target the dental industry.
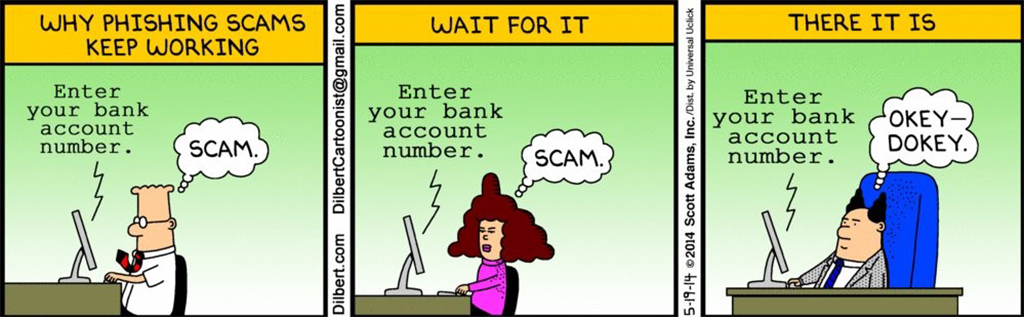
Before we begin, here's a perfect illustration of how these types of attacks still work… it's all due to high volume!
Sketchy URLs have become so common online, that most of us are uneasy clicking on links in almost any situation. So how do you stay safe? It's easy - learn how to read URLs!
#1 - Misspelling Domains
While this seems obvious, one of the most common ways cybercriminals sneak past us in phishing scams is through misspelled domains. Take a look at the URLs below and see how long it takes you to spot what’s wrong with them.
- www.pact-oen.com
- www.rnsnbc.com
- www.facebo0k.com
- www.linkedn.com
1 – Letter Scramble
When letters are scrambled inside longer words, our brains typically make the correction without us noticing.
2 – Letter Combos
Luckily, this one isn’t as common as the others due to the wide number of fonts available today. In this case, the “r” and the “n” look a lot like the letter “m.”
3 – Number Swap
If you're like the rest of us, the “o” vs. “0” issue has likely caused problems for you in some way before. It’s also a classic method used to mask a shady URL.
4 – Missing Letters
This one doesn’t always work on a number of well-known URLs, but for some longer domains, it can be very tricky to spot, especially if you're quickly scanning.
#2 – Domain Jumble
This method has become a commonly used practice for many cyber criminals in the last few years. The key thing to focus on is the top-level domain in any link before you click on it. To do this correctly, follow these two rules:
- If there aren’t any single forward-slash characters in the URL (/), then read the top-level domain from left to right.
- If there are single forward-slash characters in the URL (/), then locate which one is farthest from the right. Starting from that forward slash, read the top-level domain from right to left.
Keep in Mind:
You want to look for single forward slashes in the URL. Therefore, the double forward-slash in https:// or HTTP:// would not apply in this case.
Take a look at the URLs below - can spot which links good and which links are bad and potentially harmful:
- www.business.facebook.com/login
- https://activate.facebook.fblogins.net/8675309?login.php
- www.facebook.login.com/account
- www.facebook.com/ads/library/
active_status=all&ad_type=political_and_issue_ads&country=US&media_type=all
1 – Good!
The forward-slash is between login and com, so the top-level domain is facebook.com
2 – Bad.
The forward slash is between 8675309 and net, so the top-level domain is fblogins.net, not Facebook.
3- Bad.
The forward slash is between com and account, so the top-level domain is login.com, not Facebook
4 – Good!
The forward slash is between ads and com, so the top-level domain is Facebook.com. We’ll explain the meaning of the rest of that URL towards the end.
#3 – Short Links
Short links are more commonly used on social media and email for a number of reasons. Some of the most common resources for this are Bitly, Rebrandly, and TinyURL. Companies and marketers use these short links to reduce character counts on social media, track link clicks, etc. But because of their increased usage, they have also started to be leveraged in cyberattacks as well. Here’s an example of a short link: https://bit.ly/3fh8Dmo
So how do we protect ourselves? Thankfully, on most social platforms (especially on ads displayed in these networks), they carefully scan linked websites for authenticity, quality, and relevance to the ad itself to ensure it’s not misleading or malicious.
As for email, you do need to exercise more caution to prevent phishing scams. If the short link is being sent from a source you don’t know or trust quite yet, you can copy/paste the short link into online tools that will expand it for you. Here are some of the more popular sites for expanding short links:
UTMs & Tracking
Have you ever seen brands or businesses you often correspond with that have used links like this:
https://www.pact-one.com/insight/cybersecurity-in-2021-a-look-forward/?utm_source=blog&utm_medium=reading_urls&utm_campaign=cybersecurity_guide &utm_term=example_link&utm_content=reading_utms
First and foremost, following the single forward-slash method, you can quickly see that the top-level domain is Pact-One.com, so the rest isn’t really a concern. For those of you who are curious, here’s what it all means!
Everything after the question mark (…a-look-forward/?utm…) is simply for tracking purposes. It's designed to help businesses understand where their website traffic is coming from. In this example, here’s the information a company would gather:
- Campaign Source: Blog
- Campaign Medium: Reading URLs
- Campaign Name: Cybersecurity Guide
- Campaign Content: Reading UTMs
That’s it! UTMs can definitely be used to better mask sketchy URLs, but if you follow the best practices laid out here, they’re completely harmless.
Pact-One Solutions is constantly increasing our security measures, including the addition of the SentinelOne platform, to safeguard against phishing attacks and protect your practice. It’s all part of our commitment to making your Dental IT, Worry-Free.
To learn more about protecting you and your practice from cybersecurity threats, check out our 3 Essential Types of Cyber Security Your Practice Must Have eBook!





You must be logged in to post a comment.