Most dentists in Arizona, California, Nevada, Oregon and Washington rely on passwords to protect their patient records and limit the people who can access them. However, with the frequency of cyberattacks increasing daily and hackers getting more creative with how they infiltrate your network, passwords alone are not enough to keep them out.
Having a strong password is only the first step in securing your data. You should also use multifactor authentication (MFA) to further protect your business from a data breach.
What is MFA?
MFA is an additional authentication method that requires a user (e.g., a receptionist or dental assistant) to provide additional credentials aside from a username and password to log in to an account or network. The additional credentials can include a one-time code, a fingerprint, or even a face scan.
How does MFA prevent a data breach?
The most common way a cybercriminal can break into your company's network is through stolen user credentials. MFA can prevent this by requiring the hacker to enter additional forms of authentication. Since the hacker has no access to the other forms of authentication, the possible data breach has been successfully prevented. Here's a list of cyberattacks that MFA can stop.
- Phishing – This cyberattack uses a compromised email or link as a weapon. Hackers use phishing to trick users into clicking on a link that takes them to a fake site where they unknowingly download more malware or are prompted for their private information.
- Keylogging – In keylogging, hackers covertly install a program that tracks your keyboard activity. Keylogging is a way for cybercriminals to collect private information such as credit card numbers, login credentials, and more.
- Credential stuffing – Credential stuffing takes advantage of users who use identical login credentials across multiple accounts and platforms. Take the massive Yahoo data breach, for example. Hackers would grab one of the username-password combos and plug it into other popular sites to look for people who were too lazy to differentiate their credentials.
- Brute force attacks – In a brute force attack, hackers use a computer program to bombard a system with various combinations of usernames and passwords until it finds a combination that works.
- Man-in-the-middle (MITM) attacks – MITM attacks usually involve a hacker trying to intercept the communication of two parties to steal personal information, login credentials, spy on the user, or destroy data.
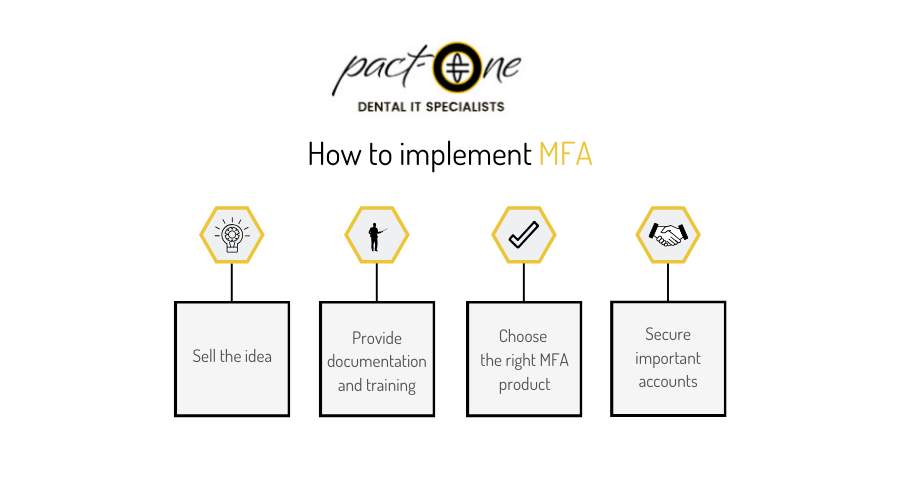
How to implement MFA
If you plan to implement MFA in your organization, you need to know what you want to protect, what MFA technology to use, and how it will affect your employees. Here are the steps on how to implement MFA:
#1 Sell the idea
Before implementing MFA in the workplace, you first need to run an internal communications campaign to inform your staff why you've decided to use MFA. You can do this by holding meetings and sending out emails.
#2 Provide documentation and training
One of the best ways for your staff to learn about MFA is by providing training sessions and documents on how MFA works, how to use it, and how your entire dental clinic can benefit from using it. We can organize a training event for you, or you can use one of these free courses.
#3 Choose the right MFA product
It's also important to choose the right MFA product for your organization. Choose one that your staff will find easy to use such as one that uses biometrics. Other factors include scalability, deployment expenses, and availability of support.
#4 Secure important accounts
Admin accounts are prime targets for cyberattacks and should be secured first. Review the role of each staff member and identify who needs to use MFA. Employees with access to patient information should be prioritized. You should also require that any mobile device with access to patient records is secured with MFA.
MFA is not a one-step solution to cyberattacks, but if properly implemented, MFA can be an effective deterrent against hackers. If you're looking to enhance your dental clinic's cybersecurity, give us a call today.
Download our free eBook!
Learn how to prevent a data breach by reading our free eBook: 3 essential types of cyber security
Dental IT. Remove the Burden. Embrace the Use.
Quality patient care – it's ultimately why you became a dental professional. But, some business operations can get in the way (such as pesky computer issues or lack of IT support). That’s where Pact-One Solutions can help! Our passion lies in supplying reliable, responsive dental IT support and security that practices can count on.
Whether you’re looking for dental IT services for your startup or searching for more responsive dental IT support – our team of dental IT specialists have you covered. With team members throughout the United States, we offer nationwide support to dental practices of all sizes. Our wide range of dental IT services ensure your data is secure, accessible, and protected.
Don't let technology challenges hinder your ability to deliver exceptional dental care. Contact us at info@pact-one.com or 866-722-8663 to join 350+ dental practices thriving with the support of a dedicated dental IT team.