Phishing continues to be one of the most effective methods of cyberattack plaguing many dental practices today. Phishing refers to a technique that involves an outside entity gaining access to private networks or data with the assistance of someone with legitimate access to them, obtained through deception and social manipulation. An administrator at a dental practice, for example, might receive an email and be tricked into opening a file that releases malware onto the practice’s network or uploads patient data to a remote server.
Phishing’s power lies in leveraging one of the most vulnerable components of any cybersecurity system: the human element. People can be extremely susceptible to exploitation, and it’s far more difficult to secure this vulnerability than to update software. This doesn’t mean, however, that there isn’t any way to prevent people from falling victim to phishing. Pact-One Solutions has compiled some telltale signs of a phishing email to help dental practices recognize and thwart potential attacks.
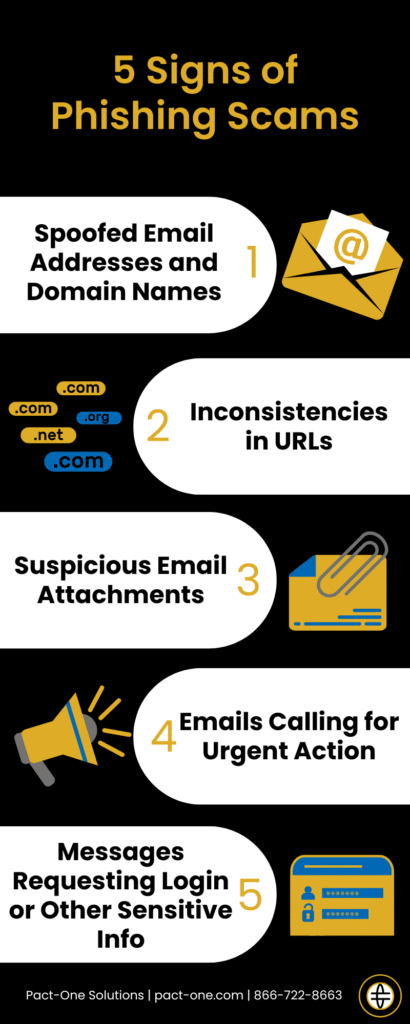
1. Spoofed email addresses and domain names
One of the most common tactics employed by cybercriminals is tricking victims into mistaking them or their correspondence with those of known or recognizable entities. They might, for example, disguise an email as one from a member of the same organization, or pose as a government agency conducting an investigation. It’s thus crucial that unexpected emails or links to websites be checked thoroughly to verify their legitimacy.
Attackers may also jumble the order of letters within a word, taking advantage of the human brain’s natural tendency to correct spelling as we read, so long as we recognize the word. For instance, cybercriminals may take inspiration from a legitimate domain name like @abcdental.com and use a similar-looking domain like @acbdental.com to fool unwitting recipients. Similarly, attackers may replace letters with similar-looking ones (capital “i” instead of “l”, “n” instead of “m”), or use numbers in place of letters (“0” for “o”).
2. Inconsistencies in URLs
Attackers may use alternate domain name endings in their URLs, such as “.net” instead of “.com”. When dealing with less familiar entities like government agencies or other businesses, these inconsistencies may be more difficult to spot than those that have been simply spoofed. If the entity the correspondence supposedly comes from has been contacted before, it may be worth comparing how the new message compares with past ones. If not, a cursory search online regarding the sender’s domain name or correspondence styles might shed light on the legitimacy of the message.
3. Suspicious email attachments
When it comes to opening files attached to emails, a good amount of common sense is vital. If users receive an email attachment from someone they weren’t expecting, they should take caution and verify the contents with IT experts before opening it.
If the sender, or supposed sender, is known, it may be worth reaching out to them in person or via a phone call to verify that the file was indeed sent by them. In lieu of that, one of the biggest telltale signs is in the attachment’s file type or extension. Some extensions like “.zip”, “.exe”, and “.scr” are commonly used for malware, and rarely for day-to-day operational use. These types of files should be automatically marked as suspicious.
4. Emails calling for urgent action
Another psychological weak point phishing attacks exploit is the impaired judgment that comes with panic. Panic can be induced with a false sense of urgency, so any emails that imply lost opportunity or warn of dire consequences if action is not taken quickly should put users on high alert. For example, phishing emails purporting to be from legitimate healthcare organizations may spread misinformation about the global pandemic to trick users into clicking on dangerous links. Other phishing scams may even offer limited-time rewards such as a free iPhone if or discounts in exchange for personal information.
Dental practices must be vigilant and not get swayed by such tricks. Any message received should be critically analyzed. The few minutes, or even seconds, needed to do a cursory check before taking action will make all the difference.
5. Messages requesting login information or other sensitive information
Generally, login credentials should never be shared via email or any other traceable method of electronic correspondence. Thus, emails that request for these, or any other sensitive information, are highly suspicious. Email is a quick and easy method of communication, but it is not known for its security. The same holds true for similar communication channels, such as instant messaging and social media. Confidential and personal information must only be shared through much more tightly guarded channels.
Phishing can be a dangerous enemy to defend against due to its exploitation of human behavior, but your dental practice can be sufficiently trained in spotting them. Call Pact-One Solutions now to get this process rolling.
Be the Dental Practice with Worry-Free IT
Giving you your time back to focus on what's most important to your practice



You must be logged in to post a comment.